Preventing NotPetya & Co. – but how?
Every attack is different
Today, companies do not have to ask themselves anymore if they will be the target of a cyber-attack but when. In more and more companies, the question is also: how often?
WannaCry and NotPetya made clear that especially the number and extent of ransomware attacks, i.e. by blackmail software, are increasing rapidly. Depending on the study, the annual growth rates are currently between 35 and 50 percent.
If production systems are interconnected with the office networks in companies, the relevant security concepts must be overhauled completely.
In addition: Every attack is different. Thus, for instance, in non-updated Windows systems, NotPetya uses the same vulnerability as WannaCry, but not exclusively. Exceeding the ETERNALBLUE gap also used by WannaCry, NotPetya is even able to copy itself onto hidden ADMIN$ directories or tries to start itself via the Windows Management Instrumentation Command line (WMIC).
While WannaCry gains access to the systems via phishing mails, NotPetya was able to do this via a software update. Also the objective seems to be a different one: While WannaCry clearly wanted to extort money, the payment function in NotPetya is designed in a very rudimentary fashion. Therefore, TÜViT also takes the view that the Trojan may be motivated politically and is used to test and see how maximum damage can be achieved to the largest possible extent. However, it is unforeseeable today what the actual target objective will later be.
Only a person guarding comprehensively against all hazards of the net, will achieve the desired digitalization successes.
Prevent rather than repair
When such an attack was successful, the first step is to implement emergency and repair measures. However, prevention is always the best defense. Therefore, TÜViT recommends preventive measures. From the start, these ensure that attackers are not able to detect vulnerabilities, which can be penetrated. If security vulnerabilities are identified and simultaneously eliminated, they can no longer be used.
Therefore, available software updates must also be loaded and installed immediately. Although there is always a danger that an update results in a new vulnerabilty opening up. However, this probability is low. In addition, a regular backup of all (important) data is recommended – if possible on an external hard drive.
IT security with a system
Whilst digitalization progresses and the number as well as the attack avenues for cyber-attacks increase constantly, a situationally driven IT security increasingly reaches its limits. It is for a very good reason that the legislator meanwhile requires companies, belonging to the so-called “Critical infrastructures“ (KRITIS), to prove an effective ISMS (information security management system).
TÜViT recommends the development and maintenance of an ISMS as a basis for a comprehensive and sustainable defense against cyber-attacks.
An ISMS clearly observes defined and standardized specifications. These have mainly been formulated in the standard ISO 27001 as well as the basic IT protection standard, the so-called “IT-Grundschutz”. Accordingly, an ISMS can also be certified according to ISO 27001. A specific ISMS mainly leads to the following:
- sustained protection of information, data and business processes
- fail-safe and reliable business and IT processes
TÜViT supports the development and maintenance of an ISMS by
- analysis and assessment of the management of information security based on ISO 27001
- gap analysis
- development of an information security process
- ISMS assessments by licensed auditors
- ISMS audits according to ISO 27001 •
- analysis of the protection requirement for the respective individual business practice
- risk assessments with regard to information security
- supplier audits
- ISMS integration into processes already existing
Information Security Management System according to ISO 27001




Checked for vulnerabilities
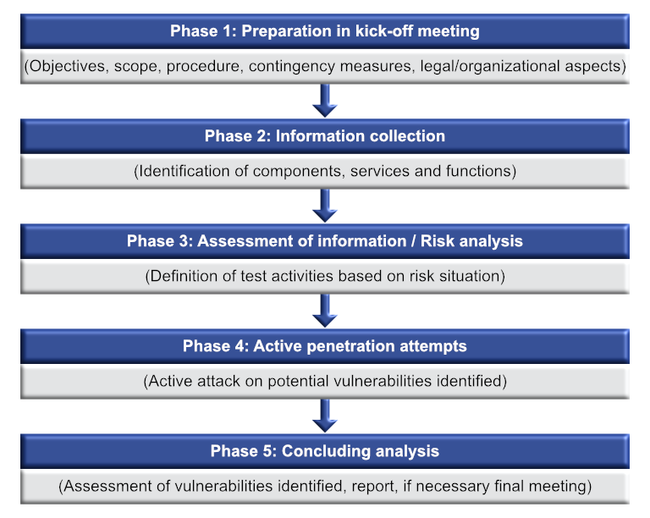
An ISMS may ensure that a company follows best practices of IT security. However, this does not ensure that the defined guidelines, measures and processes are also effective. This is the function of penetration tests. These mainly identify technical security vulnerabilities and evaluate these in a risk analysis so that recommendations for a targeted elimination can be given.
TÜViT recommends regular penetration tests as the key, with which security vulnerabilities can be detected comprehensively and then eliminated.
Penetration tests are based on a large number of different methods – and especially those also used by the attackers. So-called “ethical hackers“ target the systems the same way as actual attackers and uncover potential vulnerabilities in the same way. Among others, they check security-relevant documents and configuration settings. And they include security evaluations on the network, system and application levels as well as mobile devices, apps and industrial control systems.
Penetration testing belongs to the TÜViT core competencies.
The advantages achieved by penetration tests are numerous:
- identification of specific vulnerabilities (technical, organizational, procedural)
- objective assessment and evaluation of the effectiveness of your IT security measures
- specific recommendations for security measures, in order to eliminate the security vulnerabilities
- preparation for an internal or external acceptance procedure, audit or certification
- increasing the security awareness of employees at all hierarchy levels
- verification of the security level by means of a corresponding certificate/seal of quality as verification of trusted status toward supervisory institutions and clients
TÜViT performs penetration tests. This is one of the core competencies of TÜViT:
- the penetration tests are tailored to meet individual customer needs and requirements
- TÜViT has successfully performed hundreds of penetration tests across different industries
- TÜViT is an IT security service provider for penetration testing certified by the BSI (Federal Office for Information Security)
- the penetration tests are performed according to procedural models by recognized institutions such as the BSI
- TÜViT uses a specially developed test platform, the “Distributed Penetration Platform” (DPP)
- the DPP enables a centralized data storage even in complex network environments and increases efficiency by parallel test performance
Exemplary project schedule
Tel.: +49 201 8999-499
Fax: +49 201 8999-888
a.lange@tuvit.de